I didn’t really pick out any images out of this one, so it could contain violently graphic images of my life. Uh, not really. But it may contain things I don’t want you to see, in a third of a second. Just tell me if that’s the case, will you?
SubRosaSoft announced the release of MacLockPick recently. It’s supposedly a product for law enforcement agencies (supposedly, because there is no ‘try before you buy’ – quite a jump to take for a 600-dollar app, cough, memory stick) and it’s claimed to ‘crack any password on a Mac’.
When clicking further than the all too speculative headlines from news websites, you quickly discover some facts about MacLockPick; 1.) It’s entire working is apparently based, according to their site, to the default setting of the OS X keychain to be ‘opened’ to use. This means anyone serious enough about computer security will be able to harden themselves against it. To quote SubRosaSoft;;
MacLockPick takes advantage of the fact that the default state of the Apple Keychain is open, even if the system has been put to sleep.It also makes use of the openly readable settings files used to keep track of your suspect’s contacts, activities and history. These data sources even include items that your suspect may have previously deleted or has migrated from previous Mac OS X computers.
Oh my, we got a disaster on our hands! Macs are insecure by default! Want to prevent nasty government agencies from stealing your keychain? Read up on UNIX. Oh yeah, that advice I gave about ten times in one of the most popular OS X security how-to’s on the web also stands; any standard non-admin user will not be able to get access to those logs.
While all these statements are made here, I can honestly say I don’t know how the supposed agencies will be able to simply parse the keychain passwords to disk. If you have the keychain open, and an application tries to fetch passwords, the Keychain Agent will ask you if you want to allow access. I suppose one could automate with OSA to just ‘allow everything’, but that would really mean our implementation of the Keychain is flawed. You could also think in the sense of the InputManagers and other injection hacks that can replace such system services with their customized code (actually working example at the bottom of the page). Anyway, I’d love to get my hands on this software to see if it exploits a fundamental weakness in OS X. I am still quite sure, however, that if you follow the advice I have given in my how-to, there won’t be a slim chance in hell that MacLockPick is able to retrieve a single password from your computer. They’d have to bruteforce it.
For someone way out there.

Click here for a bigger version.
Some work with inspiration from a Futurama quote and the Matrix. “There is no two.”
I got a week of vacation coming up. I’ve still got a lot of work to do for school, but Praetorian still has a healthy amount of hours going in it every day. Some questions were raised about Praetorian recently, so I’ll post a Q&A soon. And my lecture-in-the-works for the CCC is progressing great.

Just a table content in the works, but that’s pretty much decided on. It’s up to the CCC committee to approve my paper and presentation before May 15th. So, I’m quite curious if I will make the grade.
Please keep giving input about my apps in the making! The most stupid question is the one never asked. Email’s open 24 hours a day.
Freeverse came out with Periscope, an application that, does the following;
* ‘scope your home when you’re out of town.
* ‘scope for intruders with motion detection.
* ‘scope the kids when you’re at the office.
* ‘scope a time-lapse movie of your workday.
* ‘scope for security.
* ‘scope for fun!
So, one could say this could make potential buyers or testers of iSight Expert compare the two. Before the speculation starts (and it’s bound to, since my app’s not out); there is a major difference between iSight Expert and Periscope’s design philosophy.
My application is focused on giving you control over what your iSight does; bascially, you could say it personifies a piece of hardware to do whatever the hell you want it to do; schedule it’s settings, take images on a very broad range of conditions. Perhaps the intended group of users is also different; my application has intermediate Mac users in mind with the urge to unlock their hardware potential, while Periscope looks a bit less like an application, and a bit more like a ‘game’.
In the mean time, I am in no hurry to release iSight Expert over increasing ‘competition’ — Praetorian is the application I will roll out first, and it will be followed by iSight Expert.
 The Cocoia Blog has seen a lot of hyped terms on it — but not this one yet. Say hello to the first episode of Cocoia-Cast; about Cocoa, security on the Mac, and design with Macs in general. I hope you enjoy it.
The Cocoia Blog has seen a lot of hyped terms on it — but not this one yet. Say hello to the first episode of Cocoia-Cast; about Cocoa, security on the Mac, and design with Macs in general. I hope you enjoy it.
The first episodes are about securing your communications; first securing Mail in this episode, in the second I will look at securing IM, and the third and final part will be about securing your surfing.
Link to Youtube (low res)
Download .torrent (Please do, eases the load on the server!)
Hello beta testers, time for an update.
Praetorian has been rolling steadily towards it’s Public Beta release candidate. As I have seen the trouble with compiling your own, I will make the latest sources of FreeRADIUS available as binary packages upon release, to save you the hassle. From there on, Praetorian will show you how your network’s going (the information architecture has been thrown upside down here, since the last preview) and your server is.
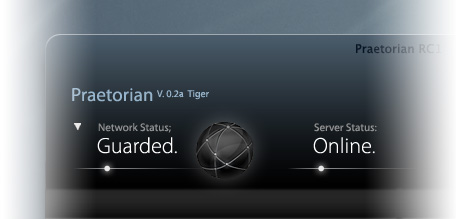
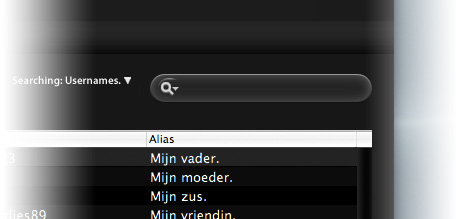
Regardless of your understanding of computers, Praetorian will allow you to set up a Mac in your network to be a RADIUS server. This means you can let people log into your wireless or wired network with a username and password, or simply filter people based on hardware (MAC) addresses.
Praetorian has assistants for these tasks built in. If you have an Airport, it’s just a few clicks away to a super-secure network.
The release candidate now has a probable release date and some features left undiscussed recently.
– New IndieHIG-compliant custom interface widgets.
– If licenses allow, a blazing fast scanning method to keep tabs on people online.
– Full document support; Praetorian’s own document type, raddb format, and SQL.
– Unlimited Undo functionality.
– Spotlight integration.
– Unparalleled security methods; passwords are stored in the keychain and kept in memory in an encrypted state.
– A separate Leopard version ready for release when OS X 10.5 is released.
Cocoia expects to start public beta as soon as June 10th, culminating with the launch of the Cocoia Beta Panel, but expects at least one pre-release candidate beta release before commencing testing on the final branch.
Sign up for beta by email
.